
Cryptocurrencies like bitcoin, litecoin, and dogecoin are increasingly becoming popular in the present times. People see cryptos as an alternative to regular currencies like the dollar and pound. Cryptos are also seen as an asset worthy of investment because the value of many cryptos, like bitcoin, is increasing rapidly.
How To Manage A Crypto Account?

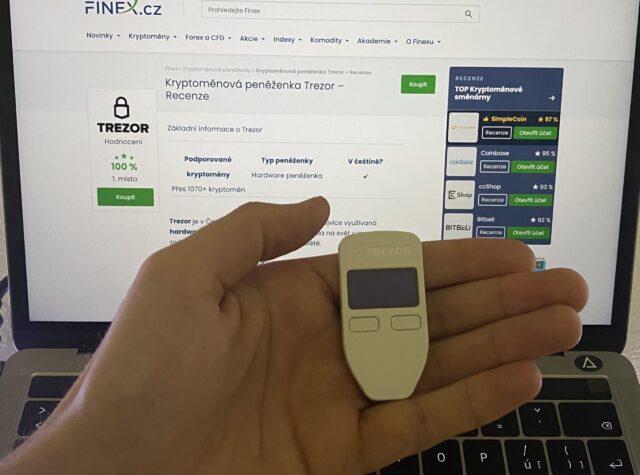
The crypto account password is the most important code that helps you in managing your crypto coins. Thus, it is vital that the account password is well protected. Hardware wallets like the Trezor One model and Trezor T model protect and store the information about your crypto account password.
You can read online blogs to learn about the differences between Trezor Model T vs. Trezor One. The Trezor One model is an older version and is quite simple to use. However, the Trezor T model is more advanced and secure. It also has an easy-to-use colorful touchscreen which makes it all the more convenient to use.
How Secure Is A Trezor One Model?
1. It Stores All The Data Offline
The Trezor One model stores all the data about a crypto account password in an offline mode. Storing data in an offline mode enhances the security of the password. When a device runs in the online mode, then it readily downloads software updates and other programs from the internet. Many of these programs can have malware.
Malware is spurious code that can deny access to a legitimate user. Moreover, it can also leak a person’s private information ( crypto account password) to scammers. Hence a data storage device that runs in an offline mode is much safer than one that runs in an online mode.
2. It Can Mask An User’s Identity
When people use their crypto addresses for making transactions like buying and selling crypto coins, then there is a possibility that other people might steal their addresses and use them in a nefarious manner. So the Trezor One model allows for identity masking.
Several techniques are used to mask the identity of a user. The actual identity may be shuffled in such a manner that it becomes almost impossible for a hacker to copy and use it. Apart from scrambling, null values may be fed in place of actual values to alter the actual identity of a user.
3. It Cannot Be Connected To Another Device Via A Bluetooth
Trezor One cannot be connected to other devices via Bluetooth. While some people may consider this to be a disadvantage because it limits the connectivity of the system but it is an advantage from the point of view of security.
Many spurious codes can be transferred via Bluetooth, and hence the inability to connect to other devices via Bluetooth can be an advantage for this hardware wallet.
4. Allows Creation Of Passphrases
A passphrase allows a user to login into a wallet that stores a crypto account’s password. A passphrase is longer than a password; moreover, a passphrase has a unique combination of spaces between two words. Also, passphrases are case-sensitive. So they are almost impossible to hack.
Passphrases add another layer of security over and above the regular password, and these greatly enhance the safety of the coded information contained in a hardware wallet.
5. It Needs To Be Connected To A Mobile Phone Or A Desktop To Work

Unlike the Trezor model T, the Trezor One has to interact with a mobile phone or a desktop to function optimally. However, interaction with a mobile phone or a desktop may introduce several vulnerabilities.
When any device is connected to a phone, then that device can acquire a virus from the phone if the phone is infected. A computer virus is similar to a biological virus. It infects a system and transforms the native codes of the newly infected system as per its own requirements.
Thus, Trezor One hardware may be safe in itself, but the fact that it has to interact with another system, like a mobile phone or desktop, increases its chances of acquiring viruses.
6. It Lacks A Backup System
The Trezor One model, unlike the advanced Trezor T model, lacks a backup system to increase the security of the wallet. The Trezor T model uses the Shamir backup system to create multiple copies of a given set of data. It uses a cryptographic method to generate multiple copies of your data. If you have multiple copies of data, that reduces the chances of data loss from your system.
On the contrary, it also increases the possibility of a copy being stolen. However, the way in which these copies are generated keeps the data safe. The copies are generated using cryptographic methods to create a 128-bit strong code. Usually, a code that is 20 characters long corresponds to 128 bits.
The user can create as many as 20 such codes. These codes can be shared with people whom the user trusts. A user can set a threshold of 3, 4, or 5 codes that he needs to recover his data. When a user needs to recover his data he can ask his trustworthy friends to share the code with him so that he can easily recover his data.
If you want to protect your data by creating multiple backup copies, then you should go for the advanced Trezor T model because the older Trezor One model does not provide the option of creating multiple cryptographic copies.
Conclusion
The Trezor One model was launched in the year 2014, but it still is quite popular among crypto users. It is easy to use, and hence it is the preferred choice of many new users. It provides adequate levels of security by allowing the creation of passphrases; it also allows users to mask their identity while making transactions.
However, there are a few limitations, like it needs to be connected to another device like a phone to carry out its functions. It also lacks a backup generation system. But overall, it provides a good level of security, it is quite affordable, and it is the preferred choice of many people even today.












